Introduction:
In today’s digital world, IT security strategy must be transformed into Business-driven security strategy to prevent failure of vital digital transformation projects.

Contents:
- Transformation to Business-Driven security
- Why Business Driven Security Model: Its importance
- Aspects of Business Driven Model:
- Conclusion:
- How Briskinfosec helps you
- Curious to read our Case studies
- Last but not the least
- You may be interested on
Transformation to Business-Driven Security:
Information Security Practitioners like security analyst and consultants of an organisation should look at Information Security from a business perspective to enforce proper risk management, so that it will be useful to prevent the data loss or assets that are most important to the organisation during the time of a threat.
For enforcing the business-driven model of Information Security in an organisation, it is essential to understand and assess the risks for the organisation in real time and then mitigating the risk, determining the incidents conclusively by a skilled incident management professional team. In short, it is critical to have a “Risk Management Team” in an Organization than a regular “Threat Management Team”.
To create a compelling business-driven security model, a business organisation must identify all of its assets, where they are placed, which assets are more vulnerable to threats and attacks etc., which will help them to categorise their holdings for the useful incident and risk management and mitigation of threats.
Why Business Driven Security Model: Its importance

The need for business-driven security arises, mainly due to the evolving threats from various aspects of technology which includes the latest trends like the Internet of Things (IoT), Artificial Intelligence (AI), Machine Learning, etc. As these new technologies evolve, the attack vector for these technologies also evolves every day.
For example, IoT devices may have vulnerabilities in firmware level and application level, which an attacker can exploit to take over the IoT device’s control, which gradually increases the threat for the owning organisation.
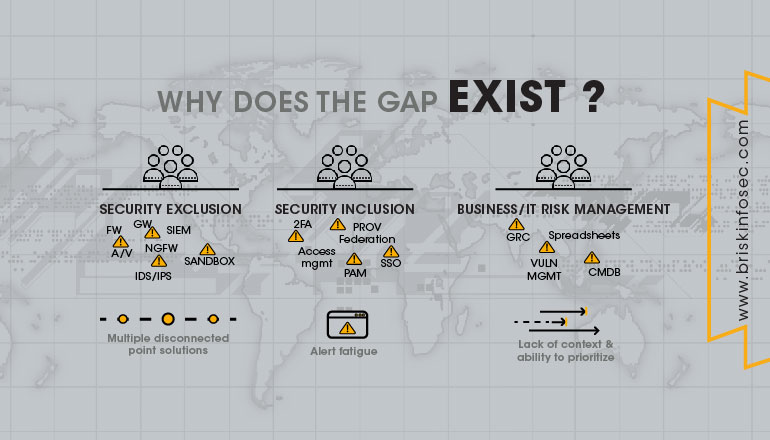
Another primary reason for the business-driven security model is “The Gap of Grief”. The Gap of Grief is a concept used to refer the void in understanding, how the security vulnerabilities can cause financial and reputation losses in an organisation. A significant part of this problem comes with the fact that the CISOs and other information security staffs in general like Penetration Testers and Consultants, fail to translate the challenges and risks in assessing a threat. In cyber-security terms, the created cybersecurity problems that aren’t effectively addressed to the right people at the right time, causes the gap of grief.
Let’s consider an example scenario: The CEO tours television and radio studios in a bid to dispel negative press and to assure the public that their data is safe with the company. This often backfires when it becomes apparent that the CEO has very little knowledge of their company's cybersecurity operations, how the breach occurred or how many customers were affected. This causes problems to the organisation, and thus the gap of grief occurs.
Aspects of Business Driven Model:
The key element of the business-driven security model is to focus more on detection, assess the threats and then on the much needed protection which is a complicated job to carry out. Then there should be a valid defence strategy specifically for all the assets and their vulnerabilities. This defence strategy should have a definite cost to benefit values assigned.
Another aspect of the business-driven security model is, it should include the required and skilled people. It must have the sufficient process and technology (Tools and services) for carrying out risk management process.
Organizations need to find out the security gaps between the current security level of their application and their infrastructure and where they want to be for an ideal security level of effective risk management. This gap analysis process is one of the key aspects to create a business-driven security model for the organisation. This gap analysis process helps out the security staffs to work on patching the gaps and vulnerabilities effectively.
Management should come up with a proper rank level for all their assets and applications based on the key values of assets. Then it will be easy for the security people to carry out gap analysis on a regular basis based on the risk ratings of assets and applications.
Conclusion:
The business-driven security model is more useful for an organisation, not just regarding cost, but also regarding proper assessment of threats and risk. If implemented in correct way, it will become an essential security model to help security people mitigate the threats and security breaches. Since it relies heavily on the risk levels for an organisation, it will help any organisation to save a lot of money and time which they were spending on the incident and threat management. So, it is exclusively your responsibility to reach out to a right security company without much procrastination before your organization gets compromised.
How Briskinfosec helps you:
Briskinfosec provides you with an effective Incident Response Team to precisely understand the type of breach incident that tarnished your business and aids you with exact needed solutions. Also, Briskinfosec assists you with its skillful Vulnerability Management Team to identify the vulnerabilities, and eliminates them swiftly. Moreover, we provide you awareness on all possible cybersecurity issues. Reach us out and your collaboration with us will leave you yearning for more.
Curious to read our Case studies?
Our stakeholders request us to perform various security assessments in order to secure their data and thwart their reputation from getting tarnished. We prove our loyalty and dexterity towards them by swiftly eliminating all the vulnerabilities through our expertise in security assessments. To know the way we shine, read our Case studies.
Last but not the least:
Whenever you’re struck by a sudden notion of checking out the latest cyberattacks that have happened worldwide, obviously you got to check in search engines. But, the biggest stress factor is the tiresome fact of checking here and there, as there isn’t a “one-click and fit-all” kind of boon, in plenty. Yes, it sounds harsh but it’s the truth. But, we have an easy solution for such searches. Just click on our Threatsploit Adversary Reports and you will find it to be a blessing, disguised as a report that has monthly collection of significant cyberattacks, happened globally.

