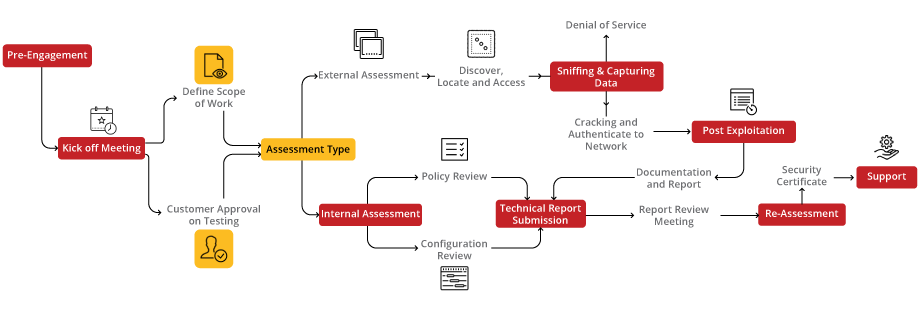
Our Wireless VA/PT Audit service ensures the robustness of your wireless network infrastructure against potential cyber threats. By conducting a comprehensive examination of wireless access points, authentication mechanisms, encryption protocols, and network configurations, we aim to identify vulnerabilities and strengthen the security posture of your wireless environment.
Our Wireless VA/PT Audit methodically examines wireless access points and network configurations to fortify your connectivity against cyber threats. Through comprehensive vulnerability scanning and encryption protocol evaluation, we ensure your wireless infrastructure remains resilient and secure.
Cybersecurity starts with proper awareness. Briskinfosec BINT LAB researchers continuously put an extraordinary effort to help you to realise cybersecurity better and faster. Just download the One-page Wireless Security flyer, Wireless Security Case Study and Threatsploit Adversary Report.
Celebrating our achievements and collaborations, shaping a future of excellence.
Our team is backed by industry-recognized certifications, ensuring top-notch cybersecurity expertise.

















Our Case studies are the best reference to prove the dexterity of Briskinfosec
Your gateway to a world of knowledge, insights, and inspiration, tailored to fuel your curiosity and broaden your horizons.
Nowadays the biggest danger that we come across and also something that we are about to face in future is The cyber threat the crime that happens via internet and technology.
Read the blogController Area Network (CAN) is the widely used In-vehicle networking. When seen from a normal point of view, CAN is really powerful in transmitting all the critical and non-critical
Read the blogRF remote controllers are used in most of the devices varying from remote control toy cars to heavy equipment’s used in mining operations and factory floor.
Read the blogElevating digital safety to unprecedented levels, setting the standard for secure online environments.
Explore the Cybersecurity Toolkits to dive into the Carousel for dynamic updates, peruse the Infographics for simplified knowledge, and view the Awareness Posters for impactful reminders. Stay ahead in the cybersecurity game!
Your gateway to a world of knowledge, insights, and inspiration, tailored to fuel your curiosity and broaden your horizons.
Expert guidance, tailored solutions- your direct path to insightful, precise answers.
Book Free Appointment
Get exclusive access to our latest Threatsploit Report detailing the most recent and sophisticated cyber attacks. Stay informed and protect your business from emerging threats.