Elevate your API security with our custom-tailored VA/PT assessments, grounded in industry-best practices and our proprietary methodologies. Through the innovative use of our LURA Portal, we offer a comprehensive security analysis, enhanced by our unique bSAFE score, providing critical insights into your API's security posture.
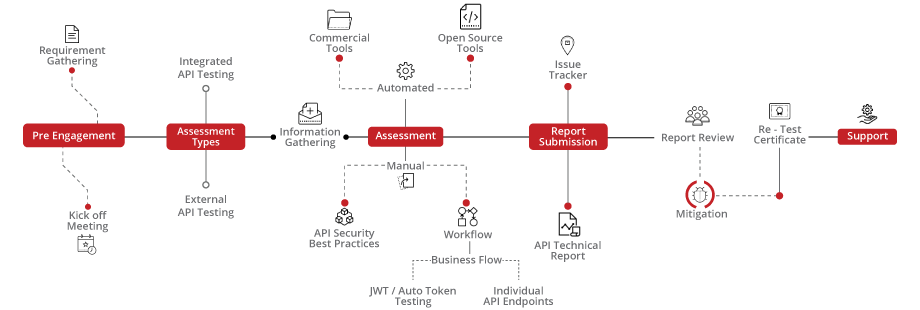
Our API VA/PT strategy offers a holistic path from initial engagement to deep-dive analysis, reassessment, and final certification, carefully designed to elevate your API security to the highest standards. This journey ensures not only technical robustness but also strategic compliance, culminating in certification that affirms your commitment to supreme cyber safety.
bSAFE delivers an in-depth maturity assessment for your API security, aligning with top industry benchmarks to foster continuous improvement and resilience.
Organizations falling into this range have a robust and secure system. Encourage continuous monitoring and periodic security assessments to maintain the high security posture.
Indicates a satisfactory security level but with room for improvement.Suggest implementing additional security measures and staying vigilant to emerging threats.
Organizations in this range are considered fragile and may have significant vulnerabilities.Recommend patches, and strengthening overall security protocols.
The lowest score suggests a system with severe security vulnerabilities. Urgently address and remediate identified issues to prevent potential breaches.




Cybersecurity starts with proper awareness. Briskinfosec BINT LAB researchers continuously put an extraordinary effort to help you to realise API security better and faster. Free download the API Security Flyer, API Security breach Case study and Threatsploit Adversary report to better understand Briskinfosec capabilities
Celebrating our achievements and collaborations, shaping a future of excellence.
Our team is backed by industry-recognized certifications, ensuring top-notch cybersecurity expertise.

















Our Case studies are the best reference to prove the dexterity of Briskinfosec
Your gateway to a world of knowledge, insights, and inspiration, tailored to fuel your curiosity and broaden your horizons.
In today's interconnected digital landscape, web applications serve as the backbone of numerous online services, facilitating everything from e-commerce transactions to social media interactions.
Read the blogNowadays the biggest danger that we come across and also something that we are about to face in future is The cyber threat the crime that happens via internet and technology.
Read the blogIn today's interconnected world, where businesses rely heavily on web applications to interact with customers.
Read the blogBrowse our selection of handy cybersecurity tools. Arm yourself with the right defenses to safeguard your digital life.
SUDO_KILLER is a tool that can be used for privilege escalation on linux environment by abusing SUDO in several ways
Read the tool of the dayMassBleed is a SSL Vulnerability Scanner that checks for TLS/SSL related vulnerabilities like Drown, POODLE, Heart Bleed, Winshock.
Read the tool of the dayAuto Scanning SSL Vulnerability which does auto Scanning to SSL Vulnerability. (HeartBleed, CCS Injection, SSLv3 POODLE, FREAK...etc).
Read the tool of the dayElevating digital safety to unprecedented levels, setting the standard for secure online environments.
Explore the Cybersecurity Toolkits to dive into the Carousel for dynamic updates, peruse the Infographics for simplified knowledge, and view the Awareness Posters for impactful reminders. Stay ahead in the cybersecurity game!
Your gateway to a world of knowledge, insights, and inspiration, tailored to fuel your curiosity and broaden your horizons.
Expert guidance, tailored solutions- your direct path to insightful, precise answers.
Book Free Appointment
Get exclusive access to our latest Threatsploit Report detailing the most recent and sophisticated cyber attacks. Stay informed and protect your business from emerging threats.