IoT Penetration Testing
End-to-end IoT security assessment - firmware analysis, hardware interfaces, wireless protocol testing, cloud backend security, and mobile app companion assessment for connected devices.
Why IoT Penetration Testing Matters
Every organization faces these critical risks. Without proper assessment, these vulnerabilities become attack vectors for adversaries.
Firmware Vulnerabilities & Backdoors
Extracting and analyzing firmware for hardcoded credentials, debug interfaces, command injection, and backdoor accounts using binwalk, Ghidra, and custom tooling.
Insecure Communication Protocols
MQTT without TLS, unencrypted CoAP, Zigbee replay attacks, and BLE sniffing. We test every wireless and wired communication channel for eavesdropping and manipulation.
Hardware Attack Vectors
JTAG/SWD debug ports, UART console access, SPI/I2C flash extraction, and side-channel attacks on physical IoT devices enabling firmware extraction and code execution.
Cloud Backend API Vulnerabilities
IoT cloud platforms with weak authentication, insecure device provisioning, missing rate limiting, and excessive data exposure through management APIs.
Default Credentials & Weak Authentication
Factory-default passwords, missing device authentication, and weak pairing mechanisms allowing unauthorized device access and control.
Supply Chain & Update Mechanism Risks
Unsigned firmware updates, unverified OTA mechanisms, and supply chain tampering enabling mass compromise of deployed IoT device fleets.
What We Assess
A comprehensive, methodical evaluation covering every critical surface area.
Deep-Dive Coverage — Every Nuance Addressed
IoT Penetration Testing isn't one-size-fits-all. Different contexts demand different assessment approaches. We go beyond generic checklists to address the specific attack surfaces and risks of each domain.
Embedded Firmware Extraction & Analysis
IoT compromise often starts long before network traffic is analyzed, at the firmware and bootloader layer where vendor assumptions are easiest to break. This domain validates whether device images, update packages, and hardware interfaces resist realistic reverse engineering.
- ▸ UART and JTAG enablement testing, fuse state verification, and debug lock effectiveness
- ▸ SPI flash dumping, chip-off workflows, and firmware carving from raw storage images
- ▸ Hardcoded credentials, certificates, and API secrets recovered from SquashFS, UBIFS, or init scripts
- ▸ Unsigned or weakly validated update package modification and malicious firmware repackaging
- ▸ Bootloader console exposure and weak authentication on recovery or maintenance modes
Device Protocol & Radio Attack Surface
IoT environments are protocol-heavy and frequently rely on weak assumptions about local trust or radio proximity. Testing covers both standards-based and proprietary communication paths that can be abused for control, persistence, or fleet-wide compromise.
- ▸ MQTT topic authorization flaws, retained message abuse, and broker trust issues
- ▸ CoAP resource exposure and DTLS downgrade or absent client authentication conditions
- ▸ BLE pairing weakness validation, GATT characteristic abuse, and insecure bonding reuse
- ▸ Zigbee or Z-Wave network key extraction and insecure join or rejoin handling
- ▸ Proprietary RF replay, rolling-code desynchronization, and frame forgery against custom devices
Cloud-to-Device Trust Validation
Modern IoT security depends on whether cloud control planes, enrollment workflows, and device identities remain bound under attacker pressure. This domain assesses whether compromise of one component can be scaled into unauthorized fleet control.
- ▸ Device identity cloning from leaked client certificates, bootstrap tokens, or manufacturing credentials
- ▸ Insecure OTA manifest verification, weak update signing, and rollback acceptance
- ▸ Broker trust abuse in shadow, twin, or digital-state synchronization workflows
- ▸ Time synchronization tampering that breaks token validation or certificate checks
- ▸ Factory provisioning flaws that leak fleet enrollment secrets into support or manufacturing channels
Safety, Persistence & Post-Exploitation
A serious IoT review must evaluate what an attacker can maintain or disrupt after initial compromise, especially where safety and telemetry are involved. The emphasis is on persistence, stealth, and the ability to pivot from a single embedded device into the broader environment.
- ▸ Watchdog bypass and boot persistence mechanisms for long-lived implants on constrained devices
- ▸ Secure boot chain weakness and measured boot gaps permitting unauthorized code to survive reboot
- ▸ Pivoting from the device operating system into adjacent LAN, OT, or cloud-connected assets
- ▸ Suppression or manipulation of logs, telemetry, and health signals sent by the device
- ▸ SBOM blind spots in bundled third-party embedded components and vendor-supplied SDKs
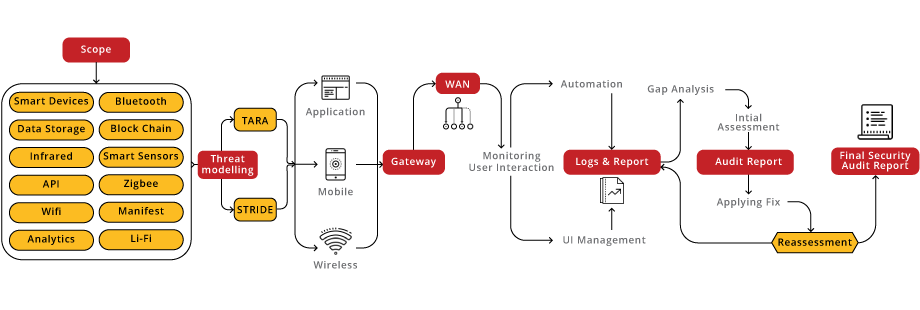
Assessment Process
A structured, repeatable methodology delivering consistent, high-quality results across every engagement.
Learn More About IoT Penetration Testing
Download our comprehensive resources to share with your team and stakeholders. Learn about our end-to-end assessment methodology and real-world success stories.
Standards & Frameworks We Cover
Why Choose Us for IoT Penetration Testing
India's Only CREST-Approved for VA & PT
International gold standard in security testing - the only Indian company with dual CREST accreditation for both Vulnerability Assessment and Penetration Testing.
Vulnerabilities Discovered
Proven track record across 5,500+ assessments. Every finding is manually validated with proof-of-concept - zero false positives.
Real-Time Project Portal
Track assessment progress, view findings, and collaborate with our team through our proprietary LURA platform. Security Simplified.
Frequently Asked Questions
Clear answers to help you make informed security decisions for your organization.
How long does the IoT Penetration Testing take?
Typically 1-3 weeks depending on scope and complexity. We provide a detailed timeline during the scoping phase based on your specific environment and requirements.
Will the assessment affect our production systems?
We use carefully controlled, non-destructive testing techniques for production environments. For invasive tests, we coordinate timing with your team and can test on staging environments.
What certifications do your testers hold?
Our team holds OSCP, CREST CRT, CEH, CISSP, and CISM certifications. Briskinfosec is CREST-approved for both Vulnerability Assessment and Penetration Testing - the only Indian company with this dual accreditation.
Do you provide re-testing after remediation?
Yes. We include one round of complimentary re-testing within 90 days to validate all findings have been properly remediated. The re-test report is provided through our LURA portal.
What deliverables do we receive?
You receive a comprehensive report with executive summary, detailed technical findings with CVSS scores, proof-of-concept demonstrations, risk-prioritized remediation guidance, and access to our LURA portal for ongoing tracking.
