Introduction
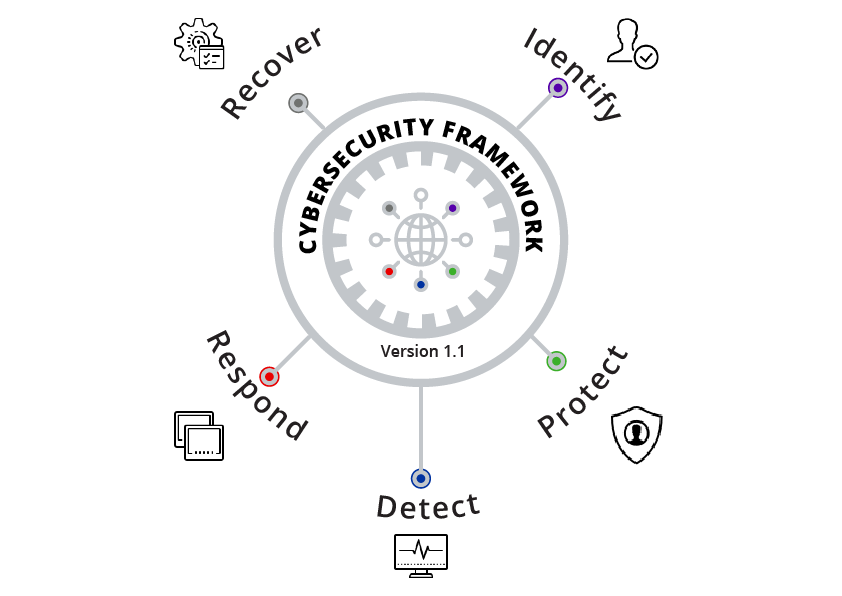
NIST (National Institute of Standards and Technology) Framework offers an agile way to address cybersecurity, including cybersecurity’s effect on physical, cyber and people dimensions. It applies to organisations relying on technology, whether their cybersecurity focus is primarily on Information Technology (IT), Industrial Control Systems (ICS), Cyber-Physical Systems (CPS), or connected devices more generally, including the Internet of Things (IoT). This framework can enhance the organisations in addressing cybersecurity that affects the privacy of their data. Additionally, the framework outcomes serves as targets for workforce development and evolutional activities.
This framework is not a ‘one-size-fits-all’ method to manage cybersecurity risk for critical infrastructure. Organizations will continue to have static risks with different threats and vulnerabilities, and also with risk tolerances. They also will vary in how they customise practices described in the framework. Organizations can determine activities that are important to critical service delivery and can prioritise investments to maximise the impact of each dollar spent. This framework is aiming to reduce the risk and produce better ways of managing cybersecurity threats.
The Framework is a living document and will continue to be updated and improved as the industry responds to implementation. NIST will continue coordinating with the private sector and government agencies at all levels. As the framework is placed into higher practice, additional lessons learnt will be integrated into future versions. It will ensure the framework meets the needs of infrastructure owners and operators in a critical environment of new threats and emerge with the swift solutions.
Contents:
- Usage of framework
- Conclusion
- Curious to read our Case studies
- Last but not the least
- You may be interested on
Usage Of Framework
An organisation can use the framework as a critical part of its systematic process for identifying, assessing and in managing cybersecurity risk. The framework is not used to replace existing methods, but companies can use its current method, and that can overlap it into the framework to determine loopholes in its current cybersecurity risk approach. The framework can be used as a cybersecurity risk management tool. An organisation can identify activities that are most central to critical service delivery and prioritise expenditures, for maximising the positive impacts of investment.
It is designed for satisfying the cybersecurity operations. It can serve as the foundation for a new cybersecurity program or a mechanism for improving an existing application. The framework provides a means of articulating cybersecurity requirements to business partners, customers and can help to identify the gaps in an organisation’s cybersecurity practices.
The framework can be applied throughout the lifecycle phases of:
- Plan
- Design
- Build/buy
- Deploy
- Operate
- Execute.
The planning phase begins the cycle of any system and lays the groundwork for everything that follows. Each and every cybersecurity considerations should be declared and described as clearly as possible. The plan should be recognized that, those requirements are to evolve during the remainder of the life cycle.
CyberSecurity Usage Framework
Conclusion
NIST Cybersecurity framework is intended to reduce risk by improving the management of cybersecurity risk to organisational objectives. Ideally, organisations using the framework will be able to measure and assign values to their risk, along with the cost and benefits of steps taken to decrease risk to proper levels. The better an organisation can estimate its risk, costs, advantages of cybersecurity strategies and actions, the more rational, useful, and lucrative its cybersecurity approach and investments will be.
Over time, self-assessment and measurement should improve decision making about investment priorities. For example, measuring, or at least robustly characterising the aspects of an organisation’s cybersecurity state and trends over time can enable that organisation to understand and convey meaningful risk information to dependents, suppliers, buyers and other parties. An organisation can accomplish this internally or by seeking a third-party assessment. If done correctly, these measurements can provide a basis for healthy trusted relationships, both inside and outside of an organisation.
Curious to read our Case studies:
Our case studies reveal you the type of security assessments, we carried out for our respectable stakeholders. Case studies stand as testify of an organization’s assessment quality. All our stakeholders are happy with our quality because of our excellence in deliverance. Check our Case studies now.
Last but not the least:
Download our Threatsploit Adversary Report and have a look at it. It will surely be a significant content, worthy in your downloads.



