Table of Contents
- Introduction
- What is the difference between security assessment and security audit?
- What is the importance of security assessment?
- Why we need external security assessment team?
- How to strengthen the internal team
- What is the cost of ignoring them?
- Conclusion
Introduction
Cybersecurity is about ensuring the safety of networks, devices and data within and outside the organization. Because of the increasing number of devices connected to the internet increases volume of data transmitted across internet also increases the cybersecurity researchers and the cybercriminal who tries to compromise the nodes and organization. Organizations should follow some of the strong policies and procedures to avoid those situations and it has become more important now than ever for organizations.
What is the difference between security assessment and security audit?
Security assessments are checks that are performed on their environment to make them secure from the external as well as internal threats, this is the step that is taken prior to an audit. Security assessment is a process of identifying the security vulnerabilities in the organization’s environments. On the other hand, security audit is an evaluation of the company’s current security posture by comparing it to an established set of policies and procedures. A security audit provides a written record of the results which provides security capabilities of the organization. The security audit characteristically gratifies the necessities of the organization based on the security standards.
What is the importance of security assessment?
Security assessment is most important part of the IT industries now-a-days, this is because that every CXO’s are wanted their organization to stay safe from the security frequent and sophisticated cyber-attacks. No matter the size of the organization or the sector in which it operates, cybersecurity has become the fast and most important concern for CIO and business leader across the globe.
So, performing the security assessment may reveal the vulnerability loopholes in the organization’s environment, which could become severe threat in the future. Security assessment may reveal the vulnerability and the exact causes for the vulnerability and helps the organization in fixing the vulnerability before any security incident occur.
Why we need an external security assessment team?
Anyone hoping to use a computer in a business environment really must take it. Many companies are aware about the assessment, also they may have a separate team for security within their organization. Sometimes trying to determine just how susceptible an organization and its infrastructure are to attack is difficult. one of the best ways to visualize a computer system—and more importantly, all of its flaws and weaknesses as seen through the eyes of a potential attacker.
Hackers are cleverer than we think. As a result, many security consulting companies and have started offering pen testing services to their clients. This kind of specialized approach is called friendly attack. Which would be a great way to evaluate the security of information systems and determine their readiness for the real virtual world.
The main objective of third-party testing is to identify weaknesses and/or security holes in all areas of an organization, from online applications to network layer to physical layer. Unlike a simple vulnerability assessment, which only identifies weaknesses, a pen test will go the extra distance by actively exploiting any holes and establishing a deeper sense of potential risk.
The vendor should then report all findings with complete honesty and transparency, as well as offer some realistic suggestions for improvement.
How to strengthen the internal security team?
Internal security team are the one in the front line of the information security. Security of the firm is always depending on them, but there are some of the reasons that organization may get failed at the security. Those are as follow:
“82% of data that was lost or stolen could have been prevented if the business followed a simple internet security plan” -Symantec Threat report
Some of the steps below may increase the strength on the internal cyber security:
Hire a Chief Information Security Officer:
CISO (Chief Information Security Officer) is responsible for setting up a security strategy and must save the organization from an evolving cyber threat. They are the one responsible for sharing their cybersecurity knowledge and advice with executives and employees, setting up an effective security plan and implementing security policies. Some of the roles and responsibilities of the CISO’s are:
- Real time analysis of immediate threats.
- Keeping an updated skill for preventing current security threats.
- Make sure the internal staff doesn’t misuse the data.
- Perform a plan for identity and access management.
- Making sure all the initiatives run smoothly and get the funding needed.

Avoiding human errors:
It might sound noticeable, but it’s very vital not to leak your company’s data, sensitive information, or intellectual property. Cybercriminals on the internet can create email addresses and websites that look legitimate. Scammers can fake caller ID information and can even take over company social media accounts and send seemingly legitimate messages.
Offer training
Training is the best way to ensure everyone in your company understands and implements your security strategy, minimizing the potential for a security incident to occur as a result of human error. Training can also help to highlight issues such as browser safety and network security, and provide employees with a general understanding of security risks. Organization should choose a right and appropriate mentor for corporate training, and should be conducted once in a year to educate the peoples of the organization to update their cyber security skills.

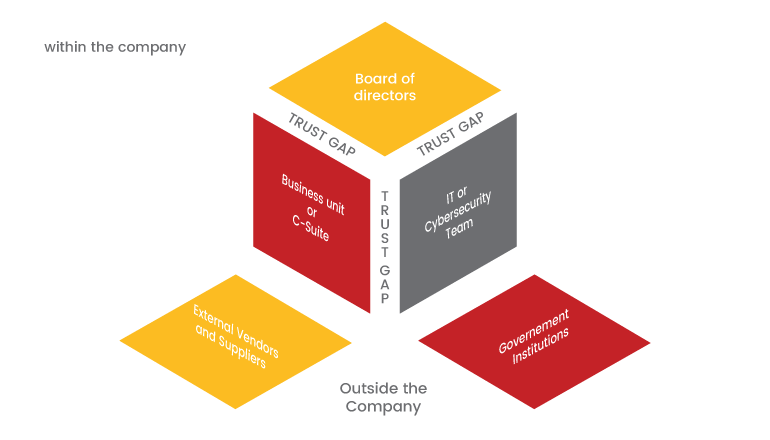
Creating a framework for improving the cybersecurity within the organization:
Protection strategies cannot be focused solely on technological controls and remediation plans. Companies must invoke the human element as well. Framework with a strategic initiative that helps prevent successful data breaches by eliminating the concept of trust from an organization’s network architecture.
What is the cost of ignoring them?
Overconfidence in the security practices and resist change or refuse to take security seriously is the one reason for an organization getting compromised. Avoiding the corporate security training may lack a clear understanding of the complexity of possible threats. Sometimes it could overestimate their cybersecurity posture or the security solutions already has in place.
Many small-scale owners find it hard to prioritize cybersecurity measures, because they don’t understand the real cost of a data breach, or because they believe that hackers won’t bother with a small scale because there’s so much more to gain by attacking a bigger enterprise. But in the reality, hackers see small businesses as an opportunity to gain quick access to unsecured data. While an attack on a larger organization might take a lot of planning and time
Consider the real cost of ignoring cybersecurity practices:
Data loss: small or larger scales industry or anything will become a target to the hackers if there is no proper implementation of cyber security solutions. In case of any type of incident which compromises the organization, the first and the major thing will be the loss of data. Hacker who has gained the access would try to gather as much of information possible.
Financial impact: Most small businesses don’t have that type of cash available for an emergency, so it can be difficult for the company to survive such an attack. Not all threats are equal; there can be a wide range in the number of individuals affected, the type of data compromised and the ways in which the company responds to the attack.
Credit damage: There’s a lot of complexity in protecting your consumer credit score, but many business owners aren’t overly familiar with it. If you tap into a line of credit to handle payroll or inventory, you’ll need to consider how a threat could impact the business.
Reputation: Even for the large scales companies an external threat which compromises their entire firm will severely affect the company’s reputation. It may take a long time for your reputation to recover. This is true if personal information, such as Social Security numbers, are stolen in a breach. Building customer loyalty following an attack can be one of the more challenging aspects of cybersecurity.
So, every organization should consider this as a main goal. Proper cybersecurity best practices will make the organization immune to the cyber threats. To avoid such kind of incidents on your organization every organization should create a training session for the employee and educate them effective on the cyber security concepts and the attack vectors. Also Chief Information Security Officer is must in planning the security measure or during the security incident.
Conclusion:
So finally, we have come to know that how an external/third party mentor and certification program is more important for an organization and what is the cost of ignoring them.



