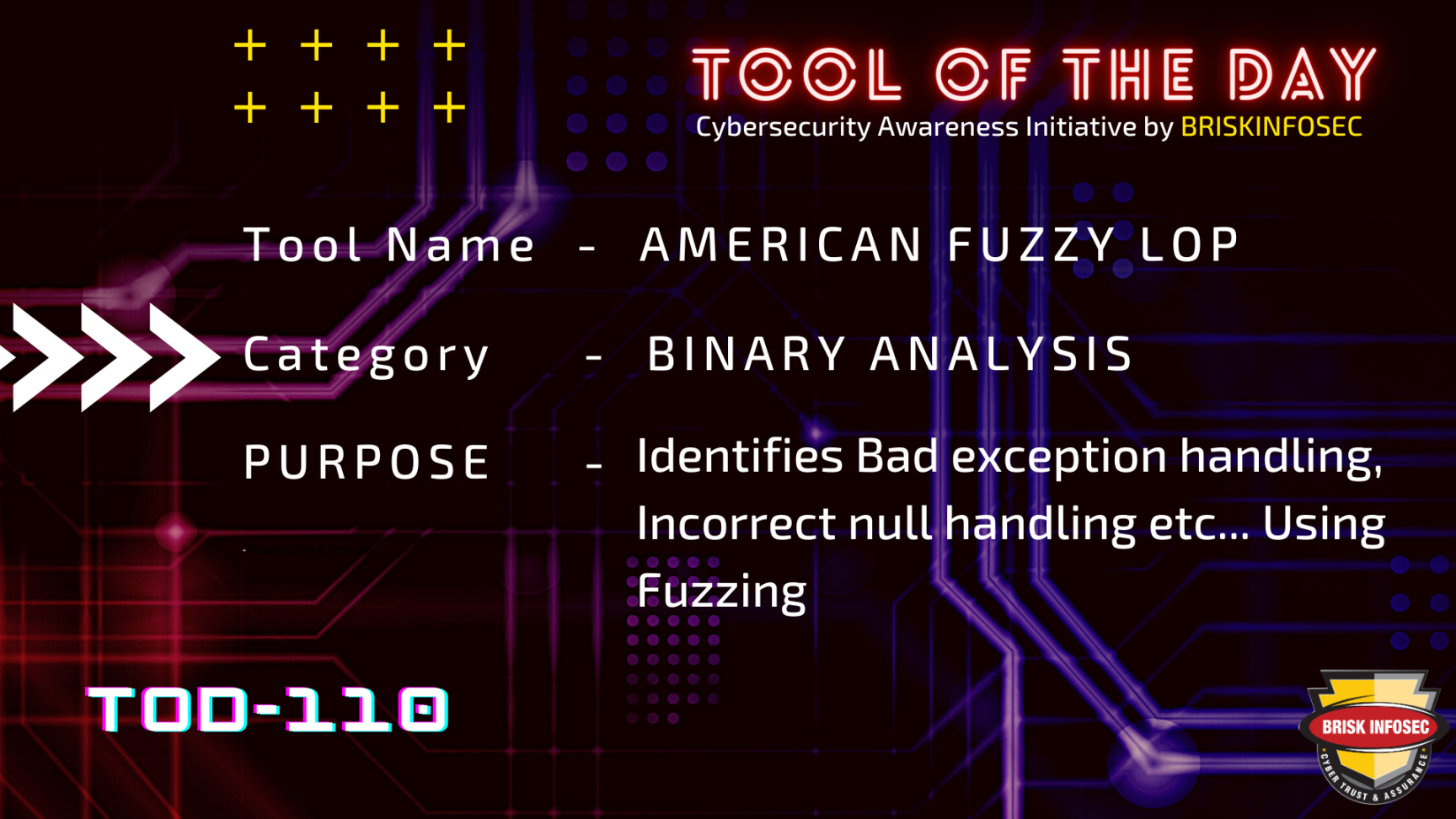
In general, Fuzzing is type of automated software testing technique that involves providing the crafted, unexpected, random or invalid data as the inputs to the computer program. Then, the program is monitored for flaws like the crashes, failing built-in-code assertions or potential memory management especially in C/C++ binaries, deadlocks, infinite loops, Undefined behaviour, Incorrect management of other resources, Bad exception handling, Incorrect null handling etc...
American fuzzy lop is security-oriented brute force fuzzer which performs a kind of complile-time instrumentation and genetic algorithms to automatically find the interesting test cases that trigger a new internal states in targeted binary programs. afl-fuzz will do the fuzzing operations automatically on the targeted binary program and it provides the interface in terminal which shows us how many crashes and hangs occurs and it will also expose some more interesting paths of the programs in run-time state while performing the automated security testing.
Demo
Installation of afl is pretty straight forward you can pull or clone it from git or if you are using the debian based OS you can make use of apt repository.
apt-get install afl
You can also get the latest release from the following instructions.
mkdir AFL
cd ~/AFL
wget http://lcamtuf.coredump.cx/afl/releases/afl-latest.tgz
tar xzf afl-latest.tgz
cd afl-*
make
sudo make install
Once the installation is done we are ready to use afl (american fuzzy lop) the main fuzzer tool afl-fuzz.
Bit about Binary Instrumentation:
Binary instrumentation is a technique that modifies a binary program, either pre-execution or during execution. This technique can be used to insert and monitoring code, such as for performance analysis, attack detection or behavior monitoring to modify program data, such as for dynamic transactional memory or to perform code replacement, such as for performance steering.
Want to know about Instrumentation:
https://en.wikipedia.org/wiki/Instrumentation_(computer_programming)
Having instrumentation in your binary program will let you know what is going on inside your binary program during it’s run-time state. It can also known as function hooking.
Want to know about function hooks:
https://en.wikipedia.org/wiki/Hooking
This unique feature makes afl (american fuzzy lop) outstanding than any other fuzzers like zzuf or peach. Because it can understand the certain point where we’d like to reach while we reaching it with the help of run-time instrumentation.
Usecases of afl:
If the target source file is available means we can compile the source with the binary instrumentation built-in for that we need to set the environment variables in our shell below with afl.
Set gcc to compile the c source files and g++ for cpp source files.
CC=afl-gcc
CXX=afl-g++
we need to create some directories for input dictionaries and output for the results of crashes, hangs and some interesting information leads to potential bugs from the binary programs.
mkdir input output
Put the dictionary file in input directory and the test results will be stored in output directory.
afl-fuzz -i input -o output /path/to/binary_file @@
@@ is a placeholder used by afl to insert the mutated payloads into the binary program.
Perhaps if the source of binary is not available to compile afl offers experimental support for fast, on-the-fly instrumentation black-box binaries. In qemu_mode by providing -Q flag with afl-fuzz.
You can use -t and -m to override the default timeout and memory limit for the executed process; rare examples of targets that may need these settings touched include compilers and video decoders.